- 1. Why are IoT devices especially vulnerable to quantum threats?
- 2. Why post-quantum cryptography matters for IoT systems
- 3. What makes quantum-safe IoT design so technically challenging?
- 4. When should IoT devices adopt post-quantum cryptography?
- 5. What does a quantum-resilient IoT architecture actually look like?
- 6. Key standards and timelines that shape quantum-safe IoT security
- 7. Quantum-safe IoT security FAQs
- Why are IoT devices especially vulnerable to quantum threats?
- Why post-quantum cryptography matters for IoT systems
- What makes quantum-safe IoT design so technically challenging?
- When should IoT devices adopt post-quantum cryptography?
- What does a quantum-resilient IoT architecture actually look like?
- Key standards and timelines that shape quantum-safe IoT security
- Quantum-safe IoT security FAQs
Quantum-Safe IoT Security: Preparing for the Quantum Threat
- Why are IoT devices especially vulnerable to quantum threats?
- Why post-quantum cryptography matters for IoT systems
- What makes quantum-safe IoT design so technically challenging?
- When should IoT devices adopt post-quantum cryptography?
- What does a quantum-resilient IoT architecture actually look like?
- Key standards and timelines that shape quantum-safe IoT security
- Quantum-safe IoT security FAQs
Quantum-safe IoT security protects connected devices from cryptographic threats posed by quantum computers.
It replaces vulnerable algorithms with post-quantum standards that can run on constrained systems. Achieving it requires crypto-agile design or preemptive deployment based on the device's lifecycle, update path, and role in the system.
Why are IoT devices especially vulnerable to quantum threats?
Cryptographically relevant quantum computers (CRQCs) don't exist yet—but their future impact on IoT security is already a concern.
The issue isn't just theoretical. It's structural. Most IoT systems weren't designed to handle the cryptographic changes that quantum computing will eventually force.
Why?
Because most IoT devices are built with hard limits on power, memory, and bandwidth.
That's what makes them affordable and scalable. But it also means they can't support cryptographic upgrades that require more power, memory, or bandwidth. Many don't even have the resources to validate firmware signatures using stronger algorithms.
And even if they could?
Most of them have no reliable way to receive updates at all.
These devices are often installed in remote or embedded environments with limited network access. Once deployed, they tend to stay deployed—with the same cryptography—for 10 to 20 years. That's far longer than today's cryptographic standards are expected to hold up against a CRQC.
This creates a major mismatch. Long device lifecycles. Short cryptographic lifecycles.
Which means:
Any IoT device deployed today with vulnerable cryptography could be exposed in the future.
Even if quantum attacks aren't practical yet. Adversaries can simply capture encrypted data now and decrypt it later. This harvest now, decrypt later model makes even low-priority devices, like smart meters, a potential risk over time.
The scale of the problem also matters.
There are billions of deployed IoT endpoints, many embedded in critical infrastructure. If they can't be updated in time, they can't be protected.
That's why quantum resilience for IoT isn't just about choosing new algorithms. It starts with understanding the long-term exposure built into how these devices are deployed.
Why post-quantum cryptography matters for IoT systems
Quantum computing poses a clear risk to the public-key cryptography used across IoT systems.
That includes key exchange, firmware signing, and device authentication. These functions often rely on RSA or elliptic curve cryptography. Both of which are vulnerable to future quantum attacks.
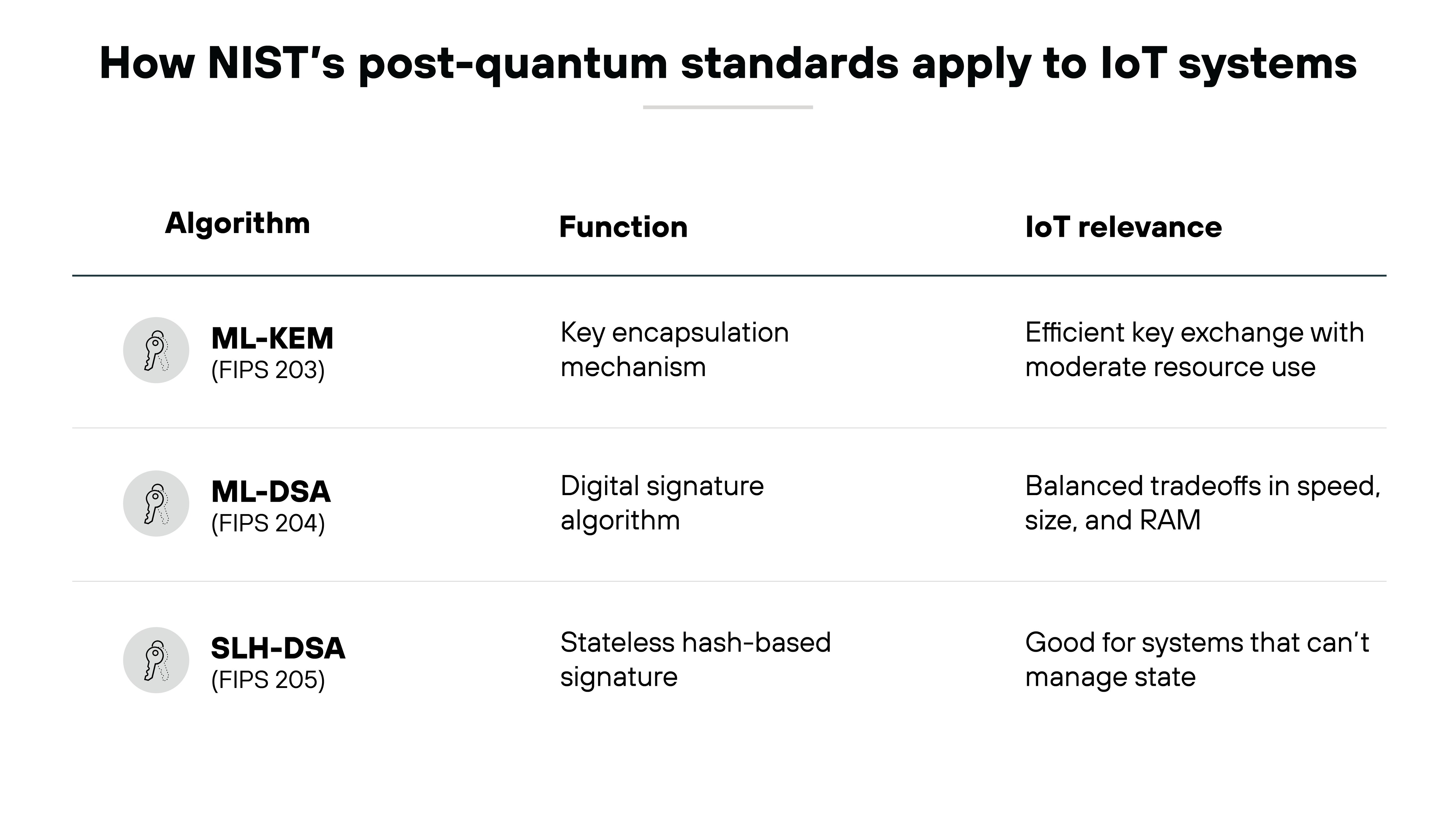
To address this, NIST has finalized three post-quantum cryptography standards. Each replaces a specific cryptographic function:
FIPS 203 defines ML-KEM, a module-lattice-based key encapsulation mechanism.
FIPS 204 defines ML-DSA, a module-lattice-based digital signature algorithm.
FIPS 205 defines SLH-DSA, a stateless hash-based digital signature algorithm.
These aren't experimental options. They're the official NIST-designated successors to widely used public-key algorithms like RSA and ECDSA.
Why this matters for IoT:
Each standard was selected with implementation constraints in mind.
ML-KEM and ML-DSA were chosen in part for their efficiency in terms of code size and memory usage. SLH-DSA provides a fallback option for devices that require stateless signature schemes. These tradeoffs directly impact whether a given algorithm can run on resource-constrained devices. Especially those with limited RAM or update bandwidth.
Important:
Post-quantum cryptography is not the same as quantum key distribution (QKD). It's implemented in software and runs on classical networks. That makes it usable today. Even in embedded systems.
For IoT manufacturers, that changes the question. It's no longer about whether PQC is coming. It's about when and how to integrate these NIST standards into real devices.
What makes quantum-safe IoT design so technically challenging?
Quantum-safe cryptography can't be retrofitted easily. Especially not in IoT systems.
The technical requirements of post-quantum algorithms often exceed what small, embedded devices can support.
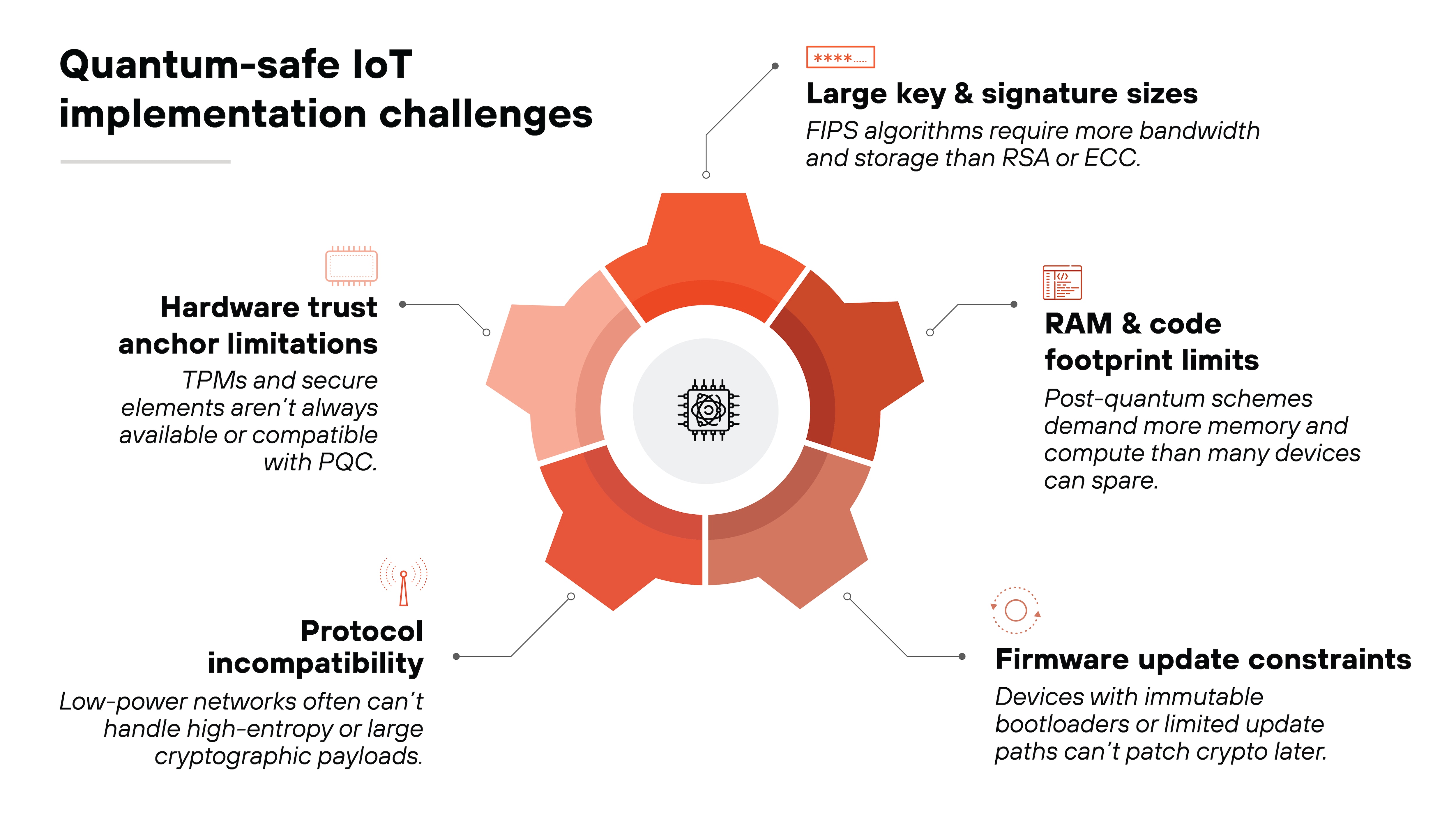
The challenge starts with key and signature sizes.
The FIPS-approved algorithms require significantly more bandwidth and storage than RSA or ECC. That creates a problem for devices already operating on kilobytes of memory and tight data caps.
Then there's the issue of RAM and code size.
Some signature schemes offer reasonable tradeoffs for mid-tier devices. But others demand more computation and storage. In highly constrained systems, that can block adoption altogether, or force a hardware redesign.
Another major challenge is firmware updates.
Many IoT devices have immutable bootloaders or no secure update path at all. If cryptography is hardcoded into read-only firmware, it can't be replaced when PQC becomes necessary. And even when updates are possible, they may fail if the device can't handle larger binaries or signature validation overhead.
Protocols matter too.
Low-power protocols aren't built for high-entropy payloads or large cryptographic exchanges. Using ML-KEM in these environments often requires significant optimization. Or fallback to crypto-agile hybrid designs.
Finally, there's hardware security.
Secure elements and Trusted Platform Modules (TPMs) can help isolate and protect PQC operations. But they have tradeoffs of their own. TPMs are rarely used in low-cost IoT. And secure elements must support the right cryptographic primitives and be compatible with PQC rollout plans.
In other words:
The barriers are not theoretical. They're implementation-specific. Which is why quantum-safe IoT design requires architectural planning, not just cryptographic compliance.
When should IoT devices adopt post-quantum cryptography?
There's no single answer for when post-quantum cryptography should be implemented in IoT devices.
It depends on the system, its lifecycle, and whether the device can be updated later. Or not at all.
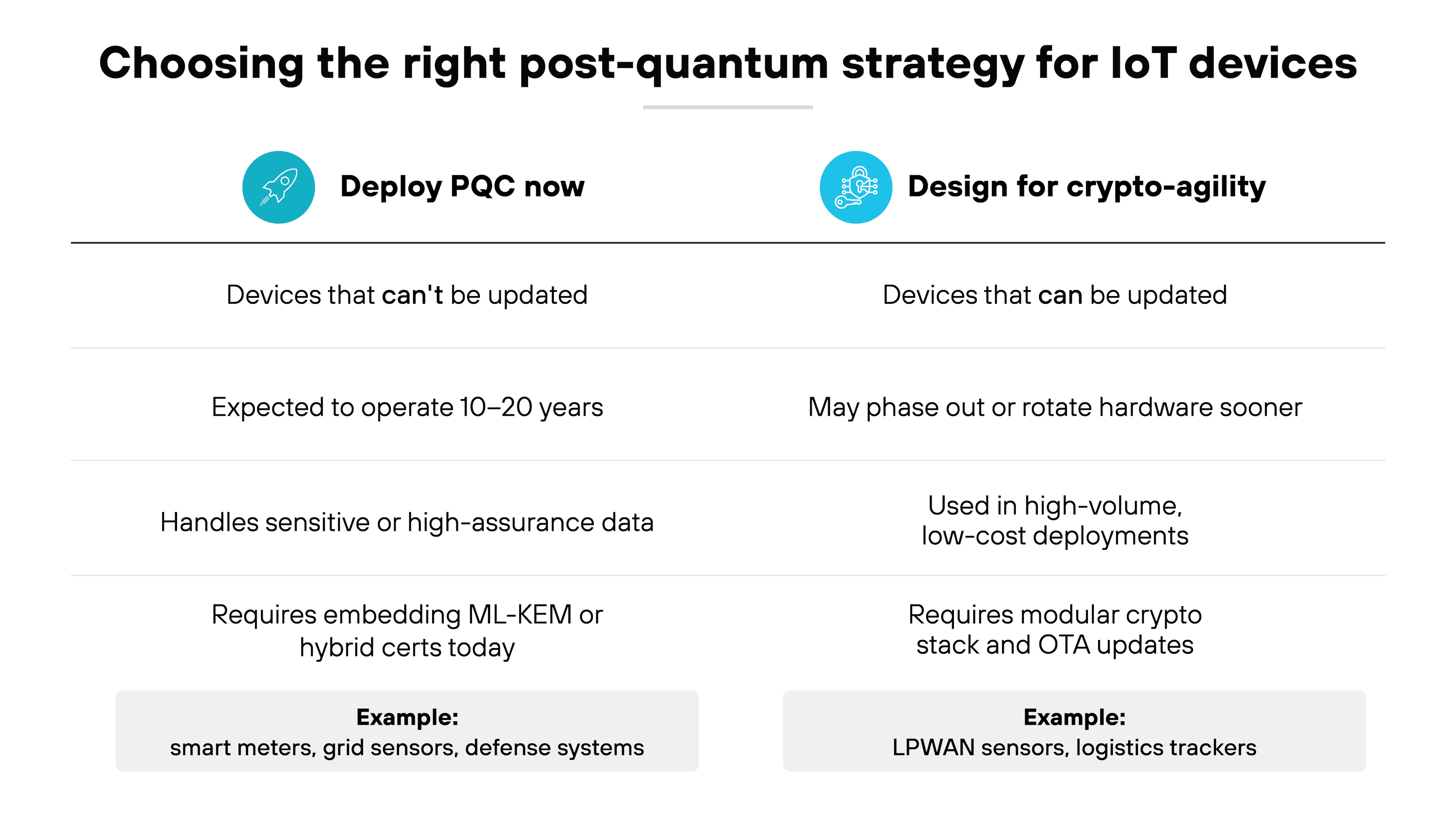
Some devices need PQC now. These are systems that are difficult or impossible to upgrade once deployed.
Think smart meters. Grid sensors. Defense applications. If a device will still be running in 10 or 20 years, and it handles sensitive data, waiting isn't a risk worth taking. These deployments benefit from embedding ML-KEM or hybrid certificates now, alongside existing cryptography.
But many IoT devices don't need to jump straight into PQC. They need to be ready for it.
That's where cryptographic agility comes in.
Designing a crypto-agile system means building in the flexibility to upgrade algorithms later. That includes having a modular protocol stack, flexible certificate handling, and a firmware architecture that doesn't hardcode cryptographic primitives.
Why not just default to crypto-agility across the board?
Because it depends on what the device can support.
LPWAN devices—like those used in agriculture or logistics—often have extreme power and bandwidth limitations. These devices may need a staged approach, where agility is built in today, and PQC is added only when the protocols and infrastructure are ready.
Industrial systems may fall somewhere in the middle.
They often support stronger compute and storage, but also run in fixed infrastructure with long certification cycles. In these cases, hybrid designs—supporting both classical and post-quantum algorithms—may offer the best balance.
Critical point:
None of this works without an update path. Over-the-air update architectures are what make crypto-agile or hybrid approaches viable. Without them, even well-designed systems can't evolve.
That's why the question isn't just about which algorithm to use. It's about how a device will adapt to future cryptographic transitions based on what it's built to do.
- Cryptographic Agility: The Key to Quantum Readiness
- What Is Hybrid Cryptography? | The Bridge to Post-Quantum Security
What does a quantum-resilient IoT architecture actually look like?
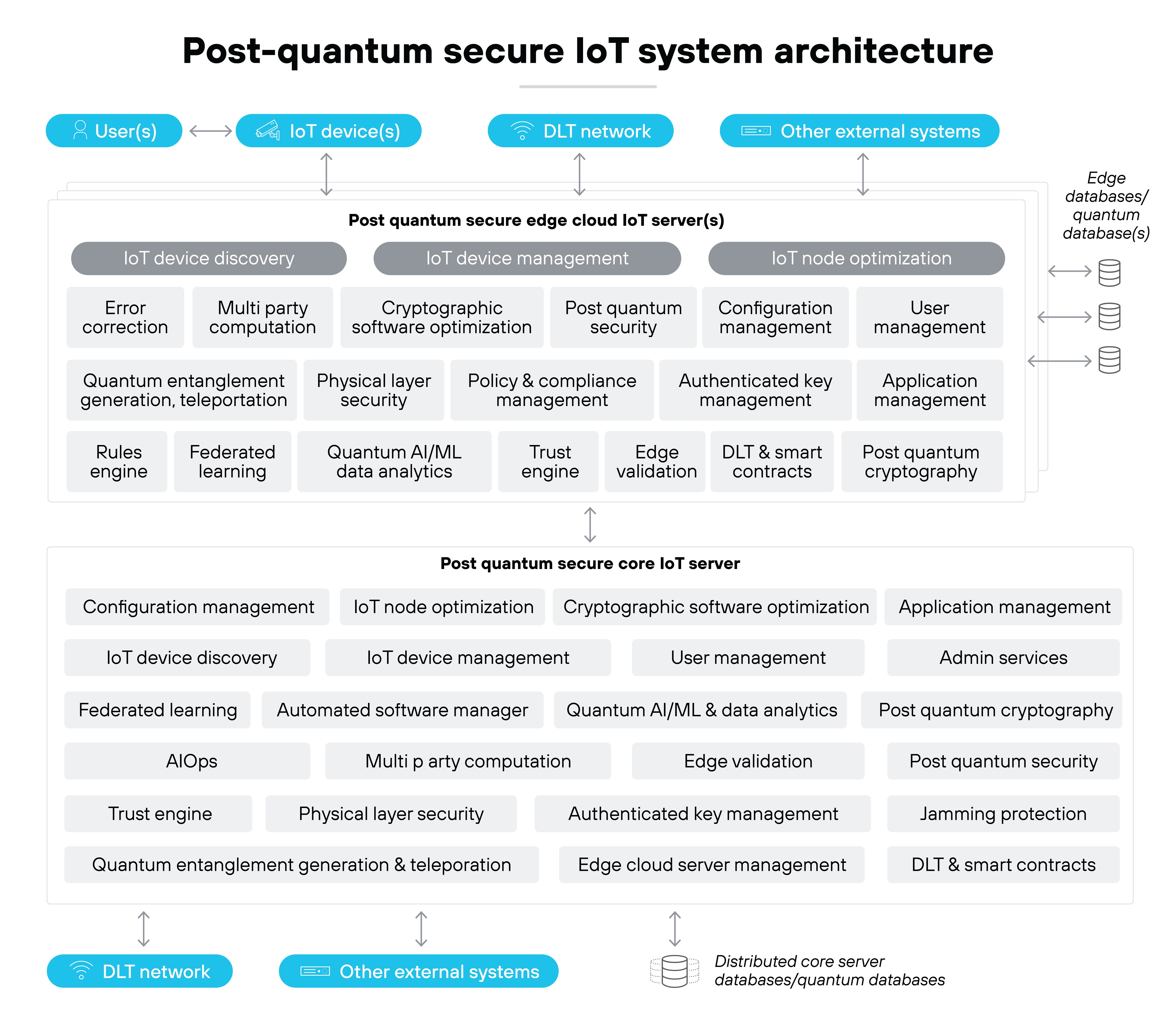
Quantum safety isn't just about picking new algorithms.
It's about building systems that can adopt, use, and update those algorithms reliably. Especially under the real-world constraints of IoT.
Start with public key infrastructure.
Many organizations will use hybrid certificates that combine a classical algorithm like ECC with ML-KEM, the NIST standard for post-quantum key encapsulation. This allows existing systems to remain compatible, while preparing for quantum risk at the same time.
It also enables gradual migration as protocols evolve.
Next comes secure identity and firmware validation.
Devices need to prove who they are and that their code hasn't been tampered with. That's where Trusted Platform Modules or Secure Elements come in.
These hardware components can isolate private keys, validate firmware signatures, and provide attestation. Especially when paired with ML-DSA or SLH-DSA, NIST's new digital signature standards.
But keys and signatures aren't useful if the protocol stack can't handle them.
Quantum-resilient IoT systems must support TLS or DTLS profiles that are compatible with post-quantum key exchange and signing.
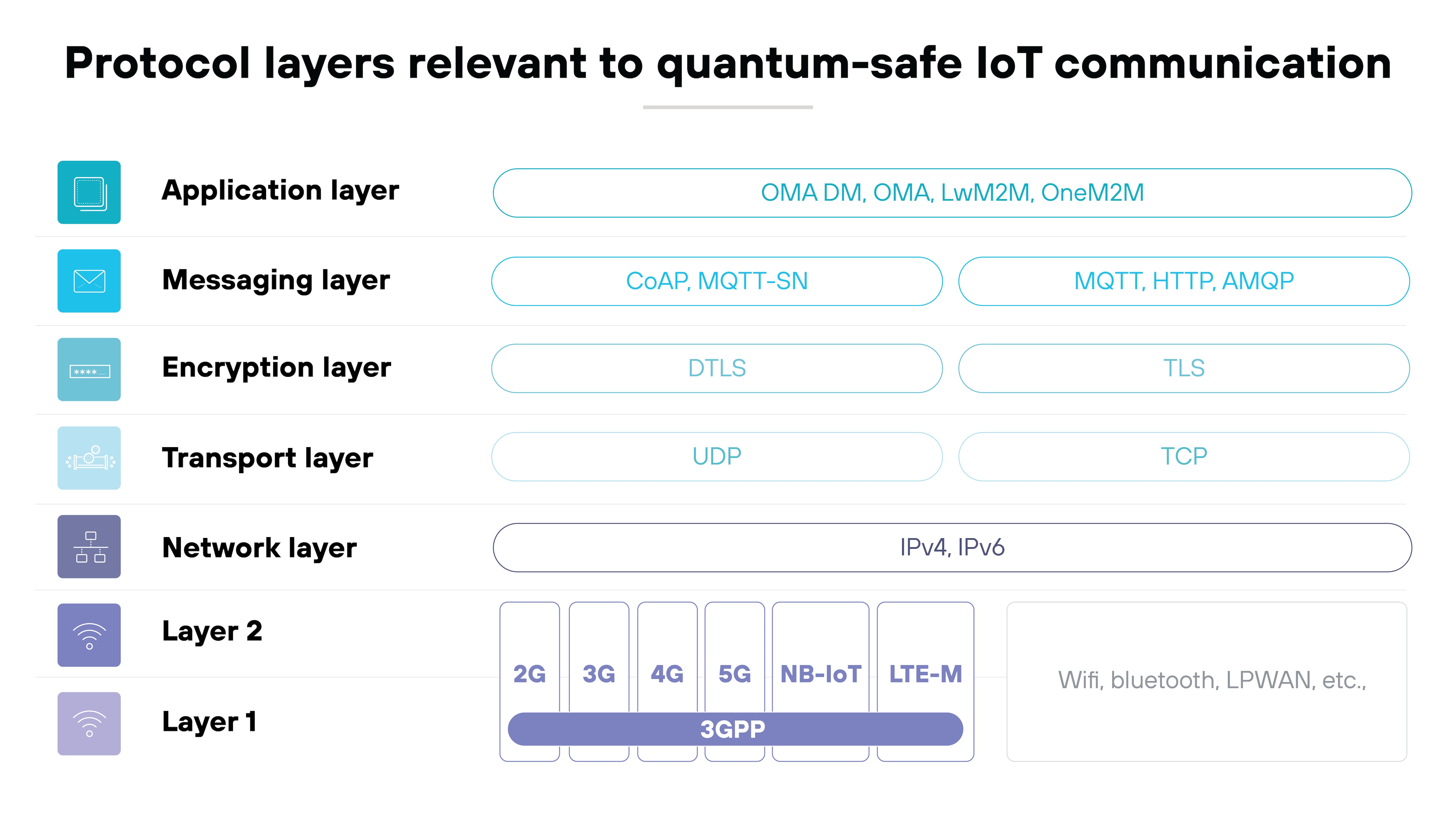
This is still evolving, but support for ML-KEM is emerging in hybrid TLS handshakes and draft DTLS proposals. For bandwidth-constrained environments, this requires testing and optimization.
And none of this works without a way to update devices.
A resilient architecture assumes cryptographic change is ongoing.
So firmware must be updatable. Certificate trust stores must be rollover-capable. And the update path must work reliably, whether over cellular, LPWAN, or local gateways.
In short:
A quantum-resilient IoT system isn't a device. It's a lifecycle. One that begins at provisioning and stretches through validation, update, rollover, and decommission. And every part of that lifecycle has to be able to adapt.
Key standards and timelines that shape quantum-safe IoT security
Quantum-safe IoT isn't just a technical challenge. It's a regulatory and compliance one, too.
Global standards bodies and government agencies have already begun issuing guidance, formal requirements, and implementation targets. These shape when and how post-quantum protections must be applied. Especially for firmware signing, device authentication, and secure updates.
Here are the standards and regulations to watch:
-
Requires post-quantum digital signatures for firmware signing in national security systems by 2025. While it applies to U.S. federal use cases, many manufacturers use it as a baseline for high-assurance devices.
-
Standardize ML-KEM, ML-DSA, and SLH-DSA. These are the formal replacements for today's asymmetric cryptographic standards. Implementation guidance is still evolving, but the algorithms are now locked.
-
Provides migration guidance specific to telecom and IoT. Outlines deployment models, protocol considerations, and transition strategies for constrained and long-lived devices.
-
Establishes cryptographic lifecycle requirements for connected products sold in the EU. Includes mandatory risk assessment, vulnerability handling, and software update policies.
IETF standards (e.g. SUIT, hybrid TLS)
Define how post-quantum cryptography fits into real-world protocols. SUIT applies to firmware update integrity. Hybrid TLS proposals enable quantum-safe key exchange while maintaining backward compatibility.
Planning target: 2030+ crypto:
Even if quantum computers aren't here yet, the lifecycle of most IoT devices means their cryptography must remain secure for 10–20 years. That means adopting or preparing for post-quantum algorithms now.
Key takeaway:
These standards aren't just abstract. They shape what post-quantum resilience actually looks like in deployed systems. And they make it clear that quantum-safe IoT isn't just a design choice. It's a timeline.