NETWORK SECURITY
Future proof your investment with faster NGFWs
Gain industry-leading, AI-powered network security and deliver real-time protection to your entire network with firewalls as dynamic as the organizations you defend. Choose from solutions for on-prem, cloud and hybrid architectures.


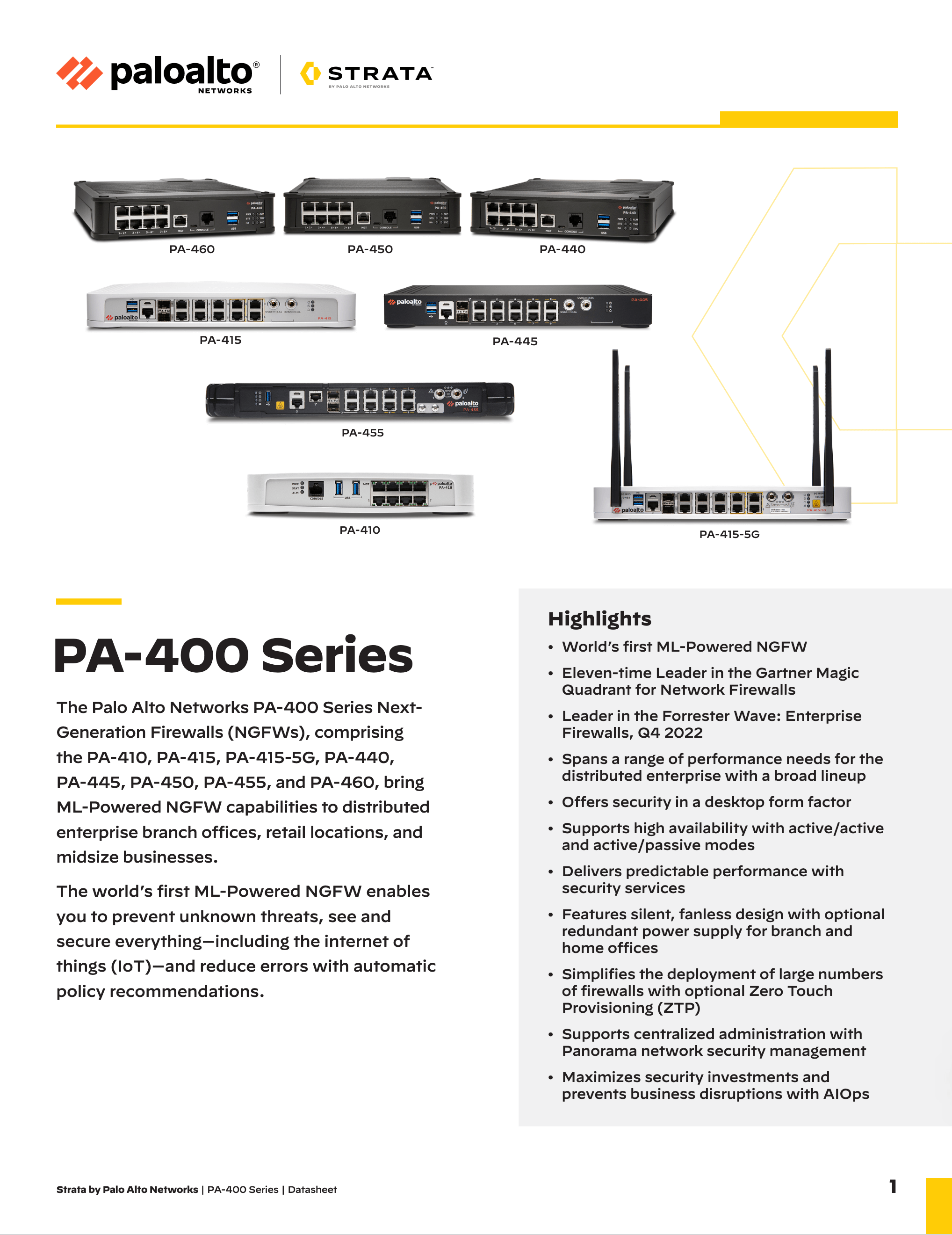
Palo Alto Networks PA-400 Series NGFW datasheet.
Platformization pays off with a 174% ROI.
Network Security Buyer’s Guide
Get hands-on with Virtual Ultimate Test Drives
SECURITY LIFECYCLE REVIEW
A complete cyberthreat assessment.
Gain clear visibility into the threats, risks and unstable applications that are bypassing your existing cybersecurity controls.
Get the details



