This post is part of an ongoing blog series examining “Sure Things” (predictions that are almost guaranteed to happen) and “Long Shots” (predictions that are less likely to happen) in cybersecurity in 2017.
Based on the trends we are seeing within the mobile industry, here are some predictions for 2017:
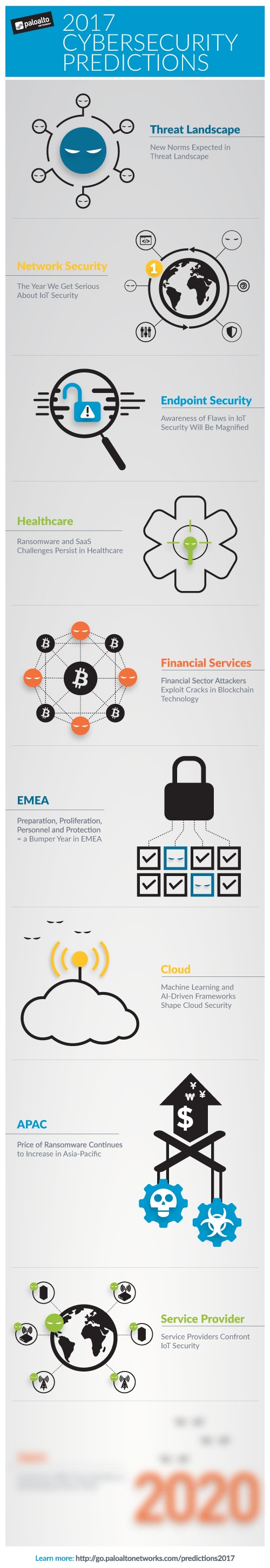
Sure Thing: Cyberattackers will target service providers by tapping into wide network of IoT devices
We have seen how IoT and wearable technology can be used by cyberattackers to launch unprecedented levels of volumetric attacks aimed at taking down specific websites and applications. These attacks will now increasingly be aimed at taking down critical service-provider network infrastructure that cause wide-scale disruptions of mobile and other connected services.Service providers will have significant pressure to shift their security posture and leverage advanced network-based mechanisms to prevent these types of malware infections from reaching IoT devices that are connected to their networks.
Sure Thing: Cyberattackers will increase their emphasis on exploiting mobile device users, and mobile device infections will exponentially increase
Consumers continue to increase their reliance on smart devices and mobile applications to manage their digital lives, making themselves easy targets for cyber criminals and creating a ripe environment for the spread of many different types of mobile malware. This trend will degrade overall trust that consumers have in their mobile services and create a new challenge for service providers, which will spur providers’ increased focus on protecting end user services and preventing potential negative impacts on their brands.“Is it the service provider’s fault” will be a common debate.
Long Shot: Cyberattacks on mobile users will become the leading cause for churn
Research has shown that consumers would rather lose their wallets than their mobile phones (and now some are using their phone as their wallet). A recent Accenture survey of smartphone users revealed 62 percent are concerned about the security of their financial transactions; 60 percent are dissatisfied with their connectivity and experience; and 47 percent are concerned about privacy and security. Altogether, a majority of them are ready to switch providers, partly because they feel their current ones don’t help safeguard their critical properties. Mobile operators will shift focus to develop new strategies that ensure the security of customer devices and prevent an erosion of customer trust that leads to lost business.
Long Shot: Service Providers will market IoT security as a competitive advantage
Over the years, service providers have tended to define network security pretty narrowly, with a prime objective of maintaining network availability and no real need or obligation to secure end user devices. This may have been sufficient for operating successfully in the past, but the landscape is now changed, with an expanding mobile attack surface and growing occurrences of infected IoT devices launching malicious attacks. The implications to service providers are significant, especially considering that IoT is being counted on to help fuel the next wave of mobile-service revenue growth; providers have no choice but to now embrace IoT security as a means of enabling future business. Who wants to be the operator that allowed a hacker to take over thousands of cars or the operator that is labelled as “less secure” than its competitor? Service providers will begin to adopt advanced network-based IoT threat prevention mechanisms, and they will begin marketing to potential IoT customers with security as a competitive advantage.
What are your cybersecurity predictions for service providers? Share your thoughts in the comments and be sure to stay tuned for the next post in this series where we’ll share predictions for Japan.