What is a Threat Intelligence Platform (TIP)?
A threat intelligence platform (TIP) is an essential tool in modern organizations' cybersecurity arsenal. It provides crucial capabilities for understanding, anticipating, and responding to cyberthreats in a timely and effective manner. TIPs have become essential organizational tools in the ever-evolving cybersecurity landscape.
A TIP provides security teams with information on known malware and other threats, powering efficient and accurate threat identification, investigation and response. It enables threat analysts to spend their time analyzing data and investigating potential security threats rather than collecting and managing data.
Moreover, a TIP allows security and threat intelligence teams to easily share threat intelligence data with other stakeholders and security systems. A TIP can be deployed as a software-as-a-service (SaaS) or an on-premises solution.

The Value of a Threat Intelligence Platform
Threat intelligence platforms offer immense value by enhancing the capabilities of security operations centers (SOCs). They aggregate threat data from various sources and transform it into actionable insights.
By comparison, a TIP helps security and threat intelligence teams:
- Automate, streamline and simplify the process of researching, collecting, aggregating, and organizing threat intelligence data and normalizing, de-duping, and enriching that data.
- Monitor and quickly detect, validate, and respond to potential security threats in real time.
- Get vital information such as background and details about current and future security risks, threats, attacks, and vulnerabilities, as well as information on threat adversaries and their tactics, techniques, and procedures (TTPs).
- Set up security incident escalation and response processes.
- Share threat intelligence data with other stakeholders via dashboards, alerts, reports, etc.
- Continually feed the most up-to-date threat intelligence data to security systems, such as security information and event management (SIEM) solutions, endpoints, firewalls, application programming interfaces (APIs), intrusion prevention systems (IPSs), and others.
How Threat Intelligence Works
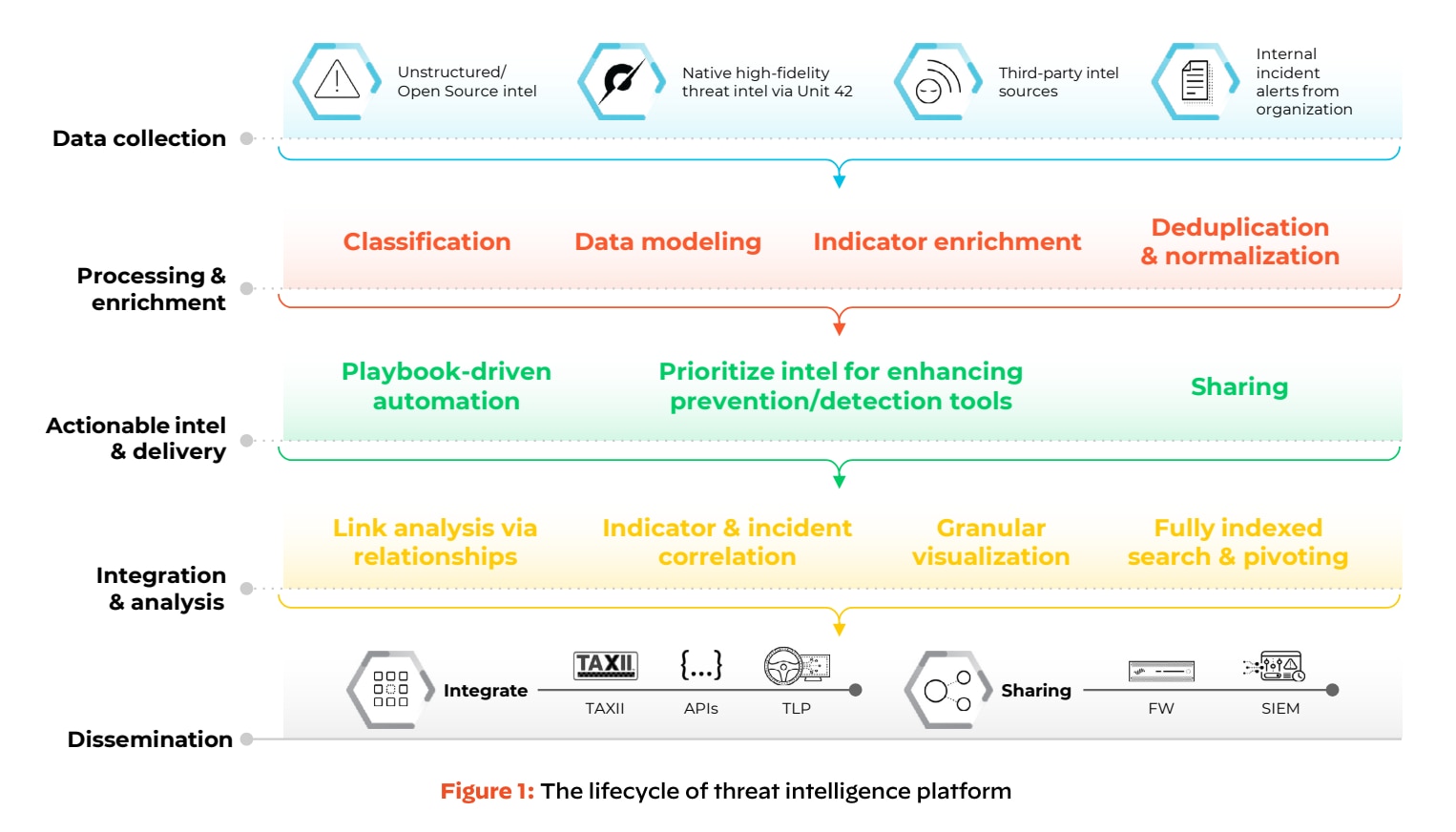
Threat intelligence in cybersecurity is a comprehensive and dynamic method that involves several stages, each crucial to developing an effective defense mechanism against cyberthreats. It starts with gathering data and extends to actionable responses, impacting how security operations centers (SOCs) operate.
Data Collection
Threat intelligence begins with collecting data from a wide range of sources. These include open-source intelligence (OSINT), such as publicly available information on the Internet, forums, social media, and specialized cybersecurity reports. Internal sources such as server logs, network traffic data, and past incident reports are also crucial.
Subscription-based intelligence feeds provide another layer of data, offering insights from industry experts, research organizations, and government agencies.
Data Analysis
The collected data is then analyzed to identify patterns (pattern recognition). This involves looking for commonalities in cyberattacks, such as similar methods used by threat actors or recurring system vulnerabilities.
Identifying anomalies is critical in threat intelligence. Anomalies might indicate a deviation from the norm, such as unusual network traffic, which could signify a security breach. Understanding the context of the data is crucial. This involves distinguishing between false positives and genuine threats and understanding the implications of a threat in the organization's specific context.
Conversion to Actionable Intelligence
The analyzed data is then converted into actionable intelligence. This means distilling the vast data into insights relevant to the organization's security posture. This intelligence aids in strategic planning, helping organizations understand their threat landscape and prepare accordingly.
Real-time Processing and Response
Real-time processing of threat data enables SOCs to identify emerging threats quickly. The faster a threat is specified, the quicker it is addressed.
Automated Responses
In many cases, threat intelligence platforms can automate responses to certain types of threats, such as isolating affected systems or updating firewalls to block malicious IPs. The intelligence also informs incident response strategies, guiding how to mitigate and recover from attacks.
Continuous Improvement
Threat intelligence is not a one-time activity but a continuous process. The insights gained from analyzing threats refine security strategies and improve defense mechanisms.
Threat intelligence is a cyclic and evolving process crucial in the cybersecurity ecosystem. It forms the cornerstone of proactive cyber defense strategies by providing SOCs with the ability to anticipate, identify, and respond to cyberthreats promptly and informally.
Types and Examples of Threat Intelligence
Threat intelligence is a multifaceted domain comprising various types that cater to different cybersecurity needs. Each type plays a unique role in providing a comprehensive view of the cyberthreat landscape.
Strategic Intelligence
Strategic intelligence offers a high-level view of the cybersecurity landscape, focusing on long-term trends and insights. This type of intelligence is crucial for decision-makers and policy developers, providing them with a broader understanding of threats, potential risks, and their impact on business or national security. Examples include:
- Global cyberthreat reports detail trends in cybercrime, nation-state activities, and advancements in cyber capabilities.
- Analysis of cybersecurity legislation and policy changes and their implications.
- Long-term risk assessments for industries or organizations.
Tactical Intelligence
Tactical intelligence delves into threat actors' tactics, techniques, and procedures (TTPs). It's instrumental for security operations center (SOC) teams and incident responders to understand how attackers operate and their strategies. Examples include:
- Detailed analysis of attack patterns and methodologies used in recent cyberattacks.
- Information about specific hacking groups and their preferred methods, such as certain phishing attacks or exploits.
- Best practices and defensive strategies to counter specific TTPs.
Operational Intelligence
Operational intelligence is concerned with specific, ongoing or imminent threats and attacks. This intelligence is highly actionable and often time-sensitive, designed to assist SOC teams in responding to active threats. Examples include:
- Real-time alerts about ongoing cyberattack campaigns.
- Information about newly discovered vulnerabilities being actively exploited in the wild.
- Incident reports and breakdowns of recent data breaches or security incidents.
Technical Intelligence
Technical intelligence focuses on the technical details of threats, such as indicators of compromise (IoCs), malware signatures, and IP addresses. IT and security teams use this type of intelligence to set up defenses and respond to specific technical threats. Examples include:
- Hash values of malware files, malicious domain names, or IP addresses associated with threat actors.
- Analysis of malware behavior, its infection vectors, and remediation steps.
- Updates and signatures for antivirus and intrusion prevention systems to detect and block known threats.
Practical Applications
- Tactical intelligence might include details about a new phishing technique, while technical intelligence would provide IoCs like malicious URLs or email addresses used in the campaign.
- Malware Analysis: Reports on new malware variants, including their behavior, attack vectors, and impact, would fall under technical intelligence, with operational intelligence focusing on current active campaigns using that malware.
- Emerging Hacking Trends: Strategic intelligence helps organizations understand the broader implications of these trends on their long-term security posture. In contrast, tactical intelligence focuses on how these trends could be applied in attacks against them.
These types of threat intelligence collectively empower organizations to understand and respond to cyberthreats on multiple levels. Strategic intelligence helps in long-term planning and policy development, tactical and operational intelligence in day-to-day security operations, and technical intelligence in dealing with specific threats and incidents.
Why Do Organizations Need a Threat Intelligence Platform (TIP)?
Since threat intelligence data frequently comes from hundreds of sources, manually aggregating this information is time-consuming. This means a technical platform is necessary to handle this task in an automated, intelligent way rather than relying exclusively on human analysts.
In the past, security and threat intelligence teams used multiple tools and processes to manually gather and review threat intelligence data from a variety of sources, identify and respond to potential security threats, and share threat intelligence with other stakeholders (usually through email, spreadsheets or an online portal).
Increasingly, this approach no longer works because:
- Companies collect massive amounts of data in various formats such as STIX/TAXII, JSON, XML, PDF, CSV, email, etc.
- Each year, the number and type of security threats (from malicious actors, malware, phishing, botnets, denial-of-service (DDoS) attacks, ransomware, etc.) continue to increase in scope and sophistication.
- Millions of potential threat indicators are spun up every day.
- Companies must respond to potential security threats much quicker than before to prevent widespread damage.
Security and threat intelligence teams are often inundated with noise and false positives. As a result, it becomes challenging for them to determine which data is the most relevant and valuable to their company. It's also difficult for them to distinguish between real and fake threats.
As a result, they have to spend more time and effort focusing on the threats that pose a genuine risk to their organization.
Key Characteristics of a Threat Intelligence Platform
Threat intelligence platforms (TIPs) provide a multi-layered approach to understanding and fighting cyberthreats. They analyze and contextualize threat information and integrate it with security operations centers (SOCs) to detect and mitigate cyber risks effectively.
These platforms' automation and response capabilities streamline the process, allowing for a more robust defense against potential cyberattacks.
Key characteristics of TIPs include:
- Data Aggregation and Integration: TIPs gather data from multiple sources, including open-source intelligence, feeds from private vendors, industry reports, incident logs, and more. This aggregation is crucial for developing a broad view of the threat landscape.
- Data Analysis: Beyond mere data collection, TIPs analyze this information to identify patterns, anomalies, and indicators of compromise (IoCs). This analysis turns raw data into actionable intelligence.
- Real-time Monitoring and Alerts: One critical function of a TIP is monitoring for threats in real time, providing timely alerts to potential security incidents, which is crucial for swift incident response.
- Contextualization of Threat Data: TIPs often provide context around the threat data, helping security teams understand the relevance of each piece of intelligence to their specific environment.
- Sharing and Dissemination: Effective TIPs facilitate intelligence sharing across different departments within an organization and, in some cases, with external entities to ensure a coordinated response to threats.
- Integration with security operations center (SOC): TIPs often integrate with an organization's SOC, providing critical inputs for security analysts and aiding in decision-making processes.
- Automation and Response: Advanced TIPs incorporate automation capabilities, enabling quicker responses to identified threats and reducing security teams' manual workload.
Types of Threat Intelligence Data
The following types of data are integral to their threat intelligence platforms. They ensure that organizations are reactive in dealing with threats as they occur and proactive in anticipating and preparing for potential future threats. This comprehensive approach is crucial for maintaining a robust cybersecurity posture in an ever-evolving digital landscape.
By leveraging these data types, threat intelligence platforms enable organizations to stay ahead in the cybersecurity arms race, ensuring a more secure and resilient digital environment.
- Indicators of Compromise (IoCs):
- Definition: IoCs are data points that suggest a network or system may have been breached. They serve as the red flags or footprints left behind by attackers.
- Examples: Common IoCs include unusual outbound network traffic, anomalies in privileged user account activity, geolocation irregularities, suspicious registry or system file changes, IP addresses, URLs, and malware hashes.
- Use: IoCs are used to detect and investigate breaches quickly. Security teams use them to scan logs and other data sources to identify malicious activity.
- Tactical Data:
- Definition: This type of intelligence focuses on threat actors' specific methods. It details attack vectors, including the tools, techniques, and procedures (TTPs) attackers use.
- Importance: Understanding tactical data helps configure security systems (like firewalls and intrusion detection systems) to defend against specific attack methods.
- Application: Security professionals use tactical data to understand and anticipate attackers' techniques, allowing them to strengthen their defenses against these methods.
- Strategic Intelligence:
- Overview: Strategic intelligence provides a high-level view of the global cybersecurity landscape. It involves analyzing long-term trends, motives, and implications of cyberthreats.
- Content: This can include insights into the geopolitical aspects of cyberthreats, emerging cyberthreat trends, changes in cyber laws, and evolving tactics of cybercriminals.
- Purpose: It aids decision-makers in formulating long-term security strategies and policies. By understanding broader trends, organizations can anticipate and prepare for future threats.
Implementation of a Threat Intelligence Platform
Implementing a threat intelligence platform is a strategic process involving several key steps, each crucial for ensuring the platform's effectiveness and alignment with an organization's specific security needs.
- Assessing Specific Intelligence Needs: Identify Objectives: Organizations must first understand their unique threat landscape and security objectives. This involves identifying the threats most relevant to the organization, the assets most at risk, and the potential impact of different threat scenarios. The focus should be on detecting, identifying, and investigating potential security threats, attacks, and malicious threat actors.
- Choosing the Right Platform: Selecting a threat intelligence platform that complements and integrates seamlessly with the existing security infrastructure is vital. The platform should be capable of aggregating and analyzing data in formats compatible with the organization's existing systems. The platform should be able to handle a variety of data formats and integrate with existing security systems like SIEM, firewalls, and intrusion prevention systems.
- Training Personnel: It is crucial to train security personnel in the technical aspects of the platform and in interpreting and acting on the intelligence provided. This involves comprehending the context of threats and how to prioritize them. It is important to regularly provide threat-related information to various teams within an organization, suggesting a multi-disciplinary approach to threat intelligence.
- Integrating the Platform: The threat intelligence platform should be integrated with existing security tools and protocols. This includes setting up workflows for the automated response and ensuring that the platform enhances, rather than complicates, the existing security operations. Best Practices include integrating threat intelligence platforms into broader security operations, including planning, monitoring, feedback, response, and remediation processes. The integration should also support automated enforcement and threat intelligence sharing across teams.
- Continuous Evaluation and Improvement: The threat landscape is constantly evolving, and so should the approach to threat intelligence. This means regularly evaluating and updating the threat intelligence platform to ensure it remains effective against new and emerging threats. The importance of staying ahead of threat actors through modernizing security systems and automating security processes, which involves continuous learning and adaptation, cannot be overstated.