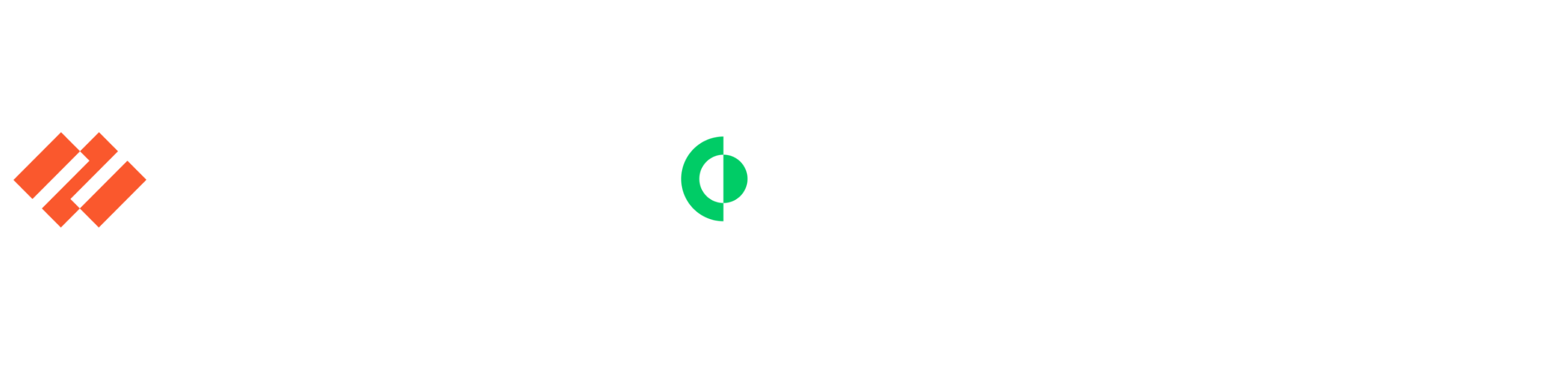
OWASP Top 10 protection
Deploying web application and API protection can be difficult in mixed environments. Prisma Cloud simplifies deployments with agent-based and agentless deployment options for all cloud-native applications, delivering full, customizable support for the OWASP Top 10.
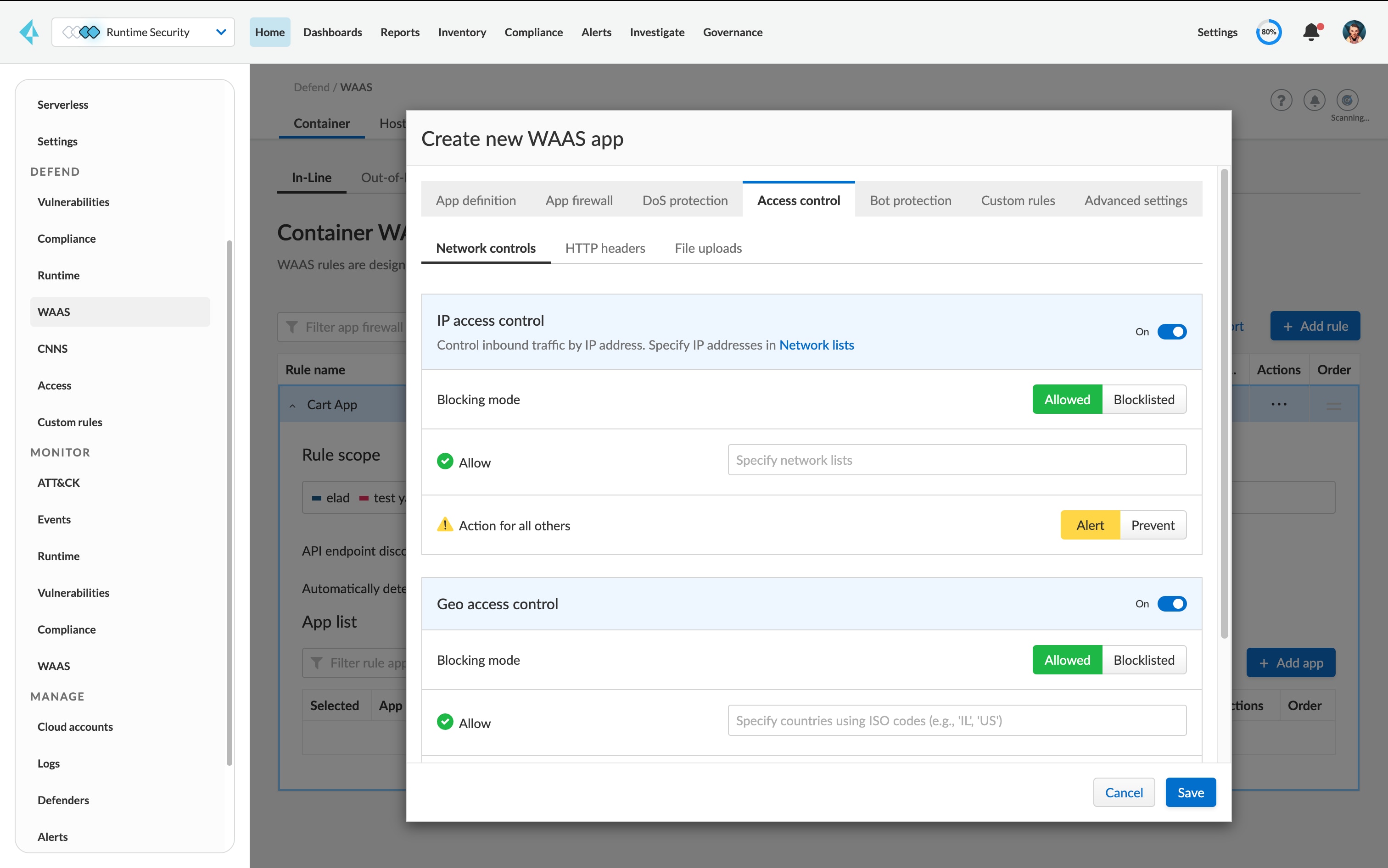
Secure web applications from top security risks:
Cover SQL injection, cross-site scripting, code injection and more.
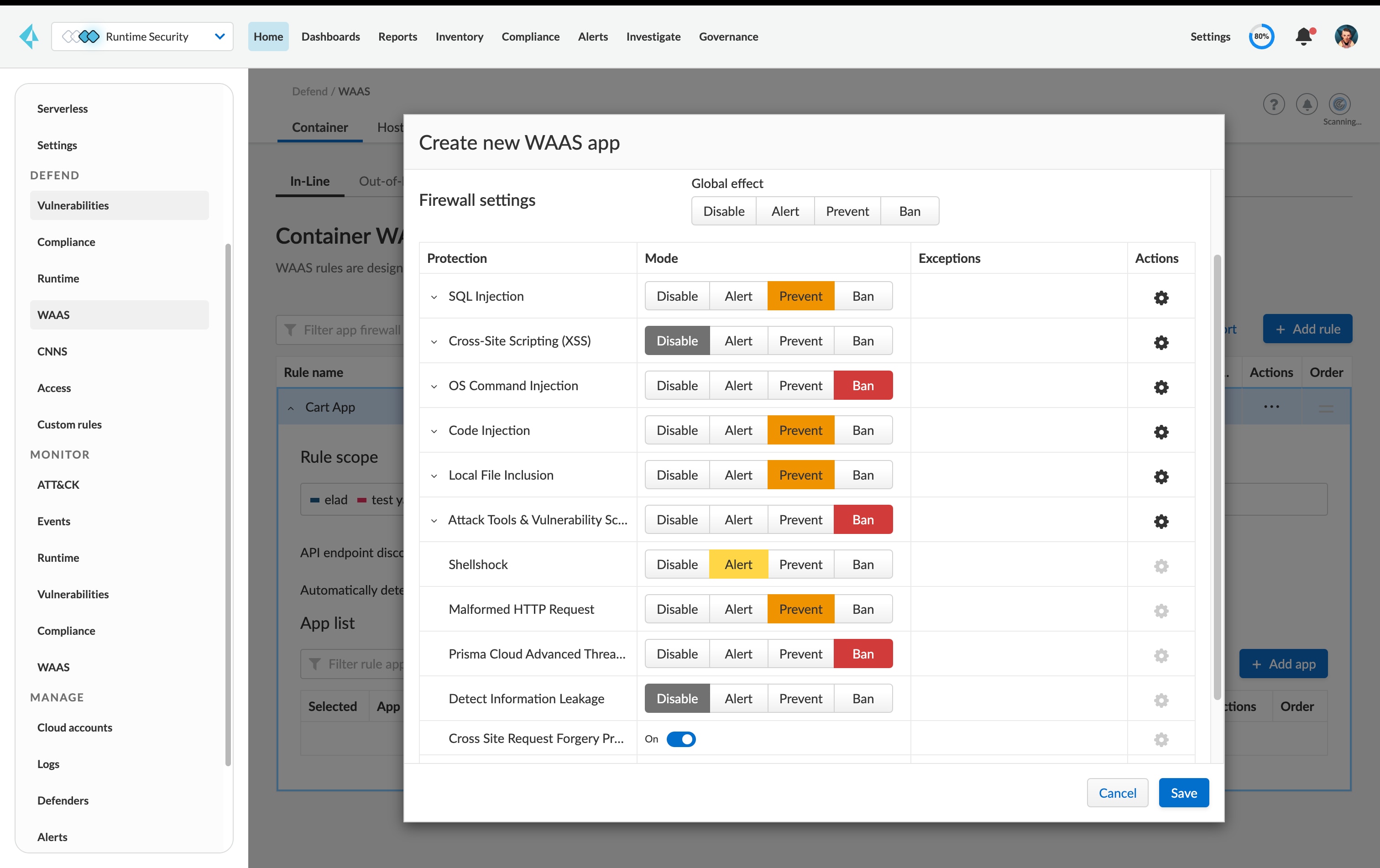
Identify applications and APIs in any compute format:
Automatically discover web-facing services and API risks to determine protection.
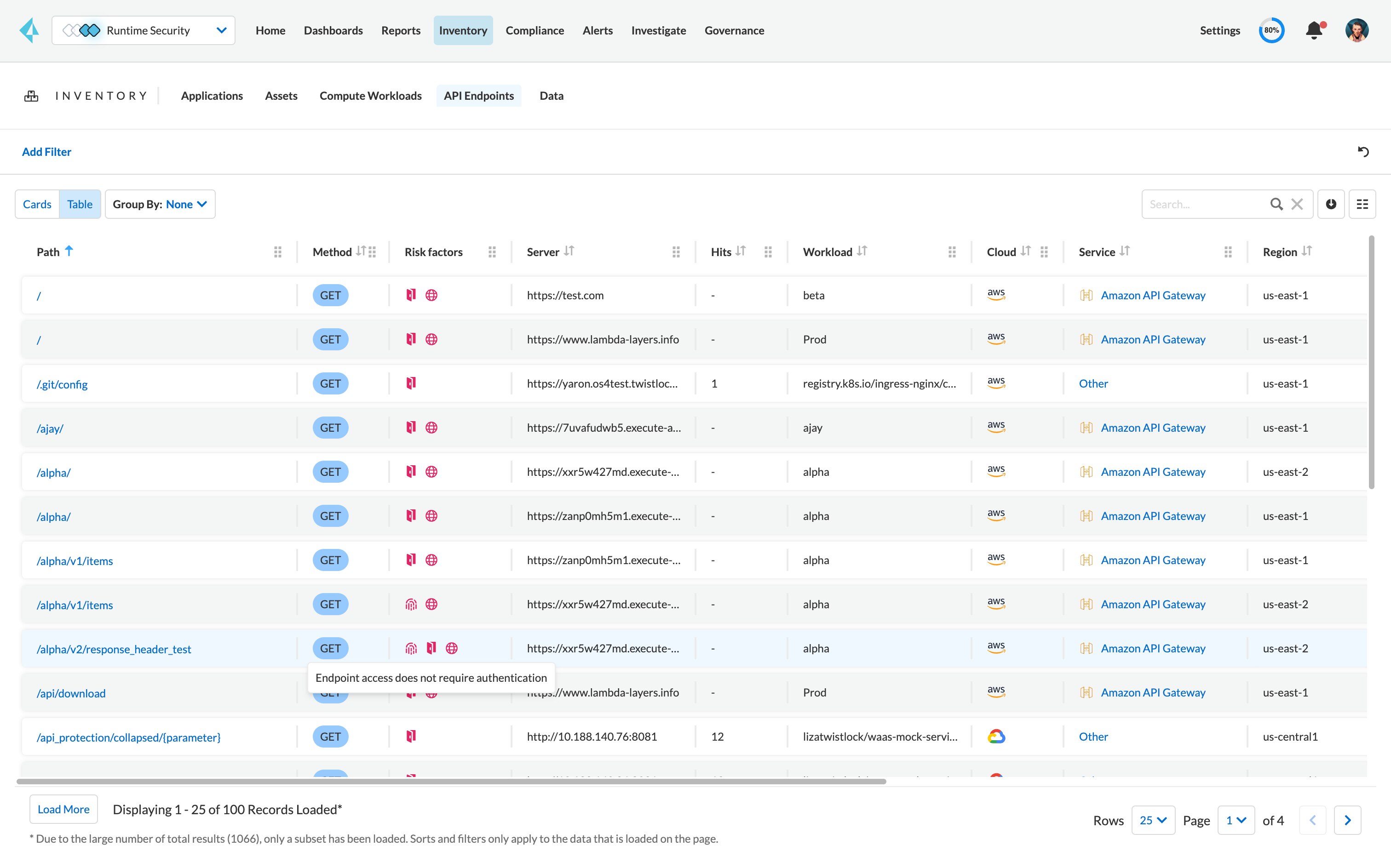
Enforce application security on microservices locally:
Automatically enforce WAAS at the service level to keep up with auto-scaling, ephemeral environments.
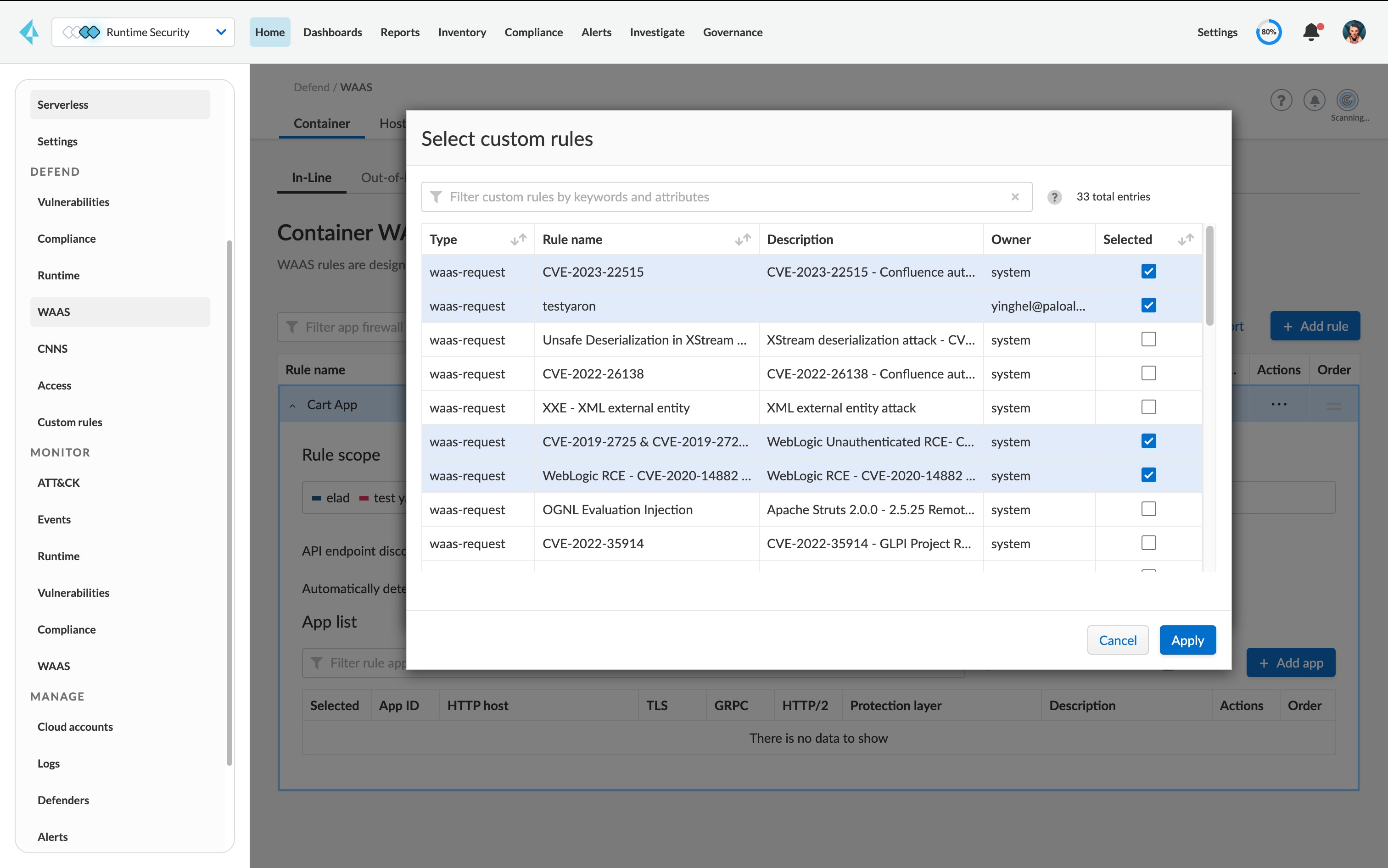
Leverage full, customizable protection:
Select which enforcement mechanism – alert, prevent or ban – to apply for each security scenario.
Deploy agents as a part of your DevOps workflow:
Use code-based deployment mechanisms to enable automatic deployment of protection with every code push.
Take a unified approach to cloud-native security:
Use a single, unified cloud security solution for superior protection compared to point products.